DMARC is one of the most important email authentication standards for modern senders. It helps protect your domain from spoofing, improves visibility into who is sending mail on your behalf, and gives mailbox providers clearer instructions when authentication fails. If you want stronger email trust in 2026, DMARC is no longer optional background work.
This guide explains what DMARC is, how it works with SPF and DKIM, what the main tags mean, and how to roll out a DMARC policy without disrupting legitimate mail.
What Is DMARC?
DMARC stands for Domain-based Message Authentication, Reporting, and Conformance. It builds on SPF and DKIM by adding alignment and policy. In simple terms, DMARC tells receiving mailbox providers what to do when a message fails authentication checks and whether that message is really allowed to use your visible From domain.
That matters because SPF or DKIM can pass in isolation without fully proving that the sender matches the brand visible to the recipient. DMARC closes that gap through alignment.
If you want the official standards background, the DMARC overview from dmarc.org is a useful external reference alongside your implementation documents.
Why DMARC Matters for Email Authentication
- Helps reduce direct-domain spoofing
- Improves visibility into legitimate and unauthorized senders
- Supports phishing defense and brand protection
- Strengthens trust with mailbox providers
- Works with SPF and DKIM as part of a complete authentication strategy
For many organizations, DMARC is the layer that turns basic authentication into an actual policy framework. It helps security teams, deliverability teams, and operations teams work from the same source of truth.
How DMARC Works with SPF and DKIM
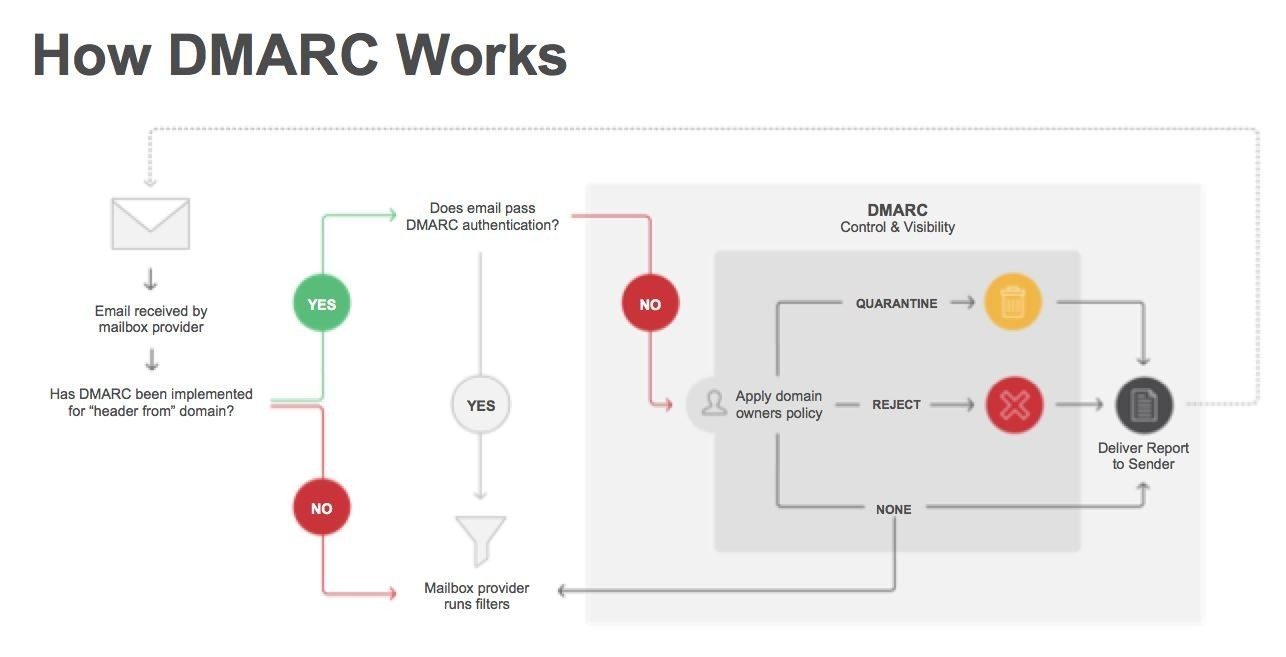
DMARC checks whether the message passes SPF or DKIM and whether at least one of those checks aligns with the From domain visible to the recipient. If the message fails alignment, the receiving system follows the policy you publish in your DMARC record.
That policy can be one of three options:
- p=none lets you monitor without changing delivery behavior
- p=quarantine asks receivers to treat failing messages more suspiciously, often by sending them to spam
- p=reject asks receivers to reject unauthenticated, non-aligned messages
The best way to think about DMARC is as an enforcement layer. SPF and DKIM provide signals. DMARC decides how those signals should be trusted when the visible brand identity is involved.
DMARC Alignment Explained
Alignment means the domain checked by SPF or DKIM should match, or appropriately relate to, the From domain shown to the recipient. Without alignment, a message can technically pass a check while still misrepresenting the sender identity.
This is why DMARC is so effective against domain spoofing. It forces the authentication result to connect with the brand identity that the user actually sees.
Common DMARC Record Tags
- v: protocol version, usually
DMARC1 - p: requested policy for the domain
- rua: address for aggregate reporting
- ruf: address for forensic reporting where supported
- pct: percentage of messages subject to the policy
- sp: policy for subdomains
- adkim: DKIM alignment mode
- aspf: SPF alignment mode
Not every deployment needs every tag on day one. But you should always understand who receives the reports and how the policy will apply to your real mail streams.
A Basic DMARC Record Example
A simple monitoring record may look like this:
v=DMARC1; p=none; rua=mailto:dmarc@example.comOnce you understand your legitimate senders and alignment is stable, you can move gradually toward stronger enforcement.
How to Implement DMARC Safely
1. Validate SPF and DKIM first. DMARC depends on them. If those records are incomplete or misaligned, DMARC reports will be noisy and enforcement will be risky.
2. Publish a monitoring policy. Start with p=none so you can see who is sending mail using your domain.
3. Review aggregate reports. Identify legitimate platforms, shadow IT, forwarders, and unauthorized sources.
4. Fix alignment issues. Work through every sending platform until legitimate sources pass correctly.
5. Move toward quarantine and reject carefully. Stronger enforcement is valuable, but only after your sending ecosystem is mapped and controlled.
DMARC Best Practices
- Keep a clear inventory of every tool that sends on behalf of your domain
- Review DMARC reports regularly, not just once
- Use separate subdomains when it helps isolate mail streams
- Coordinate between deliverability, security, and infrastructure teams
- Document policy changes before moving to enforcement
- Re-check alignment after migrations or new vendor rollouts
If you are still building the broader authentication stack, review the foundation first: SPF explains sender authorization, while DKIM explains message signing.
What DMARC Does Not Solve
DMARC is not a full deliverability guarantee. It does not automatically fix poor list hygiene, weak content, low engagement, or spam complaints. It strengthens trust and identity protection, but you still need responsible sending practices.
That is why authentication should always be paired with reputation management, list quality, and a consistent email strategy.
Final Thoughts
DMARC helps modern senders protect their domains, reduce spoofing risk, and gain more control over authentication. The best rollout starts with visibility, improves alignment, and then moves carefully toward enforcement.
If your domain matters to your brand, DMARC should be treated as a core email standard, not an optional technical extra.