DKIM is one of the core email authentication standards behind trusted email delivery. It helps receiving systems verify that a message was authorized by the sending domain and that important parts of the email were not altered in transit. If you want to improve domain trust, reduce spoofing risk, and support better deliverability, DKIM matters.
This guide explains what DKIM is, how it works, why it is useful, and what senders should understand before implementing or troubleshooting it.
What Is DKIM?
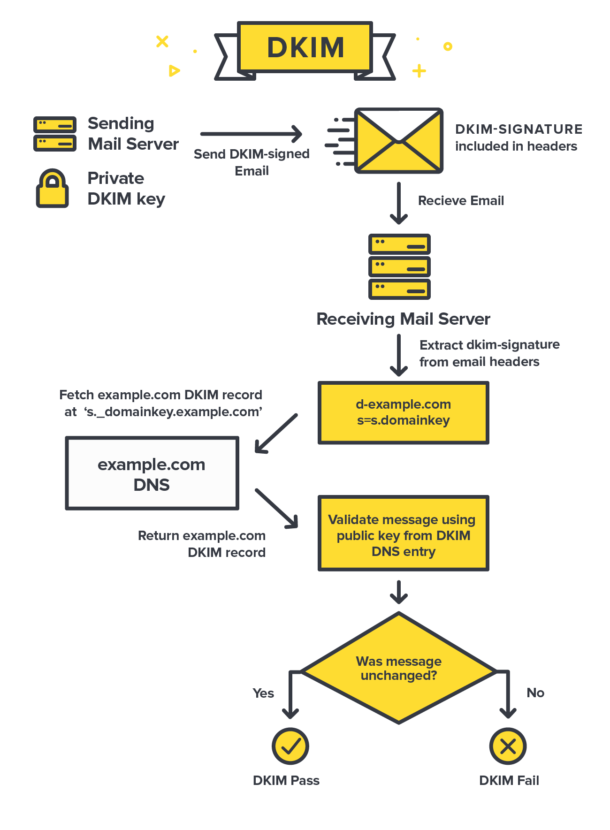
DKIM stands for DomainKeys Identified Mail. It is a signature-based email authentication method that allows a sender to attach a cryptographic signature to an email. Receiving servers can then use a public key stored in DNS to verify that the signed parts of the message were authorized by the domain and were not changed after sending.
In practical terms, DKIM helps prove message integrity and domain responsibility. It does not encrypt the message body for privacy, but it does help prove that the message is legitimate from an authentication perspective.
For the underlying standard, the official DKIM specification in RFC 6376 remains the best technical reference.
Why DKIM Matters for Email Authentication
- Helps mailbox providers trust the sending domain
- Supports domain reputation over time
- Reduces the risk of certain spoofing and tampering scenarios
- Works with SPF and DMARC as part of a layered authentication setup
- Improves control over how your domain is recognized in the email ecosystem
On its own, DKIM is not the whole deliverability story. But without it, modern authentication is incomplete, especially for brands sending significant email volume.
How DKIM Works in Email Authentication
DKIM uses a public-private key pair. The private key stays with the sending server or email platform. The public key is published in DNS under a selector. When an email is sent, the sender signs parts of the message using the private key. The recipient server retrieves the public key from DNS and verifies the signature.
If the signature validates, the receiver knows the message was authorized by that domain and that the signed content was not modified after sending.
Key DKIM Components and Selectors
- Selector: identifies which public key in DNS should be used
- d= domain: shows the domain that signed the message
- Signature header: contains the values used to validate the message
- Public key in DNS: allows receivers to verify the signature
- Private key: securely signs outgoing mail on the sender side
A typical DKIM DNS record looks like a TXT record under a subdomain such as selector._domainkey.example.com. Your ESP or mail platform usually provides the exact value.
What DKIM Does and Does Not Do
DKIM does: verify message integrity, show domain-level authorization, and support better domain trust.
DKIM does not: guarantee inbox placement, replace list hygiene, or encrypt the content of your email for confidentiality.
This distinction matters because many senders assume DKIM alone will solve deliverability issues. It will not. It is one critical layer, but it works best alongside SPF and DMARC.
How to Implement DKIM
1. Get the DKIM record from your email provider. Most ESPs and mail platforms generate the selector and public key for you.
2. Publish the record in DNS. Add the TXT record exactly as instructed. Small DNS formatting errors can break validation.
3. Enable signing in the sending platform. Some tools publish the key but still require separate activation for outgoing mail signing.
4. Test the signature. Send test messages and confirm DKIM passes in message headers or authentication reports.
5. Monitor after changes. Re-check DKIM after migrations, subdomain changes, or vendor replacements.
DKIM Best Practices for Domain Trust
- Use domain-aligned DKIM where possible
- Rotate keys according to your security policy
- Keep an inventory of all platforms signing on your behalf
- Separate streams by subdomain when it improves operational control
- Review authentication results after infrastructure changes
- Pair DKIM with DMARC reporting for better visibility
Common DKIM Problems and Validation Issues
- Incorrect DNS formatting or incomplete records
- Wrong selector being queried
- Messages modified in transit in a way that breaks signature validation
- Platform changes that disable signing unexpectedly
- Alignment issues when multiple systems send from the same brand
If authentication is correct but inbox placement is still weak, compare the issue with your list quality and engagement signals. This broader guide on improving email deliverability can help connect authentication with operational fixes.
Final Thoughts
DKIM is one of the foundations of trusted email. It helps prove that your messages were authorized by your domain and arrived without unauthorized changes. While it does not solve every deliverability problem, it plays a major role in modern authentication and long-term sender trust.
If your brand depends on email, DKIM should be implemented carefully, monitored regularly, and treated as a core part of your infrastructure.